It’s amazing what you can find inside the RAM on embedded devices using a JTAG! I’m currently dumping the RAM image of an energy usage monitor. So far I’ve seen OpenVPN keys and a few other interesting files still in memory. With any luck I’ll get a copy of /etc/passwd 😉
Category Archives: Reverse Engeneering
More DroboPro FS fun
I’ve been playing around with my old DroboPro and in the process managed to frag the uBoot config rendering the unit basically useless as the vxWorks side didn’t boot the special disk applications required for correction function. Â Fortunately I have another Drobo, in this case a Drobo FS. Â I was able to disassemble that (I …
Drobo Pro/FS
After working through it a bit more it appears that the problem is actually in the Drobo Dashboard. Â For some reason it is refusing to show the “Drobo ProFS”. Â I loaded up the 1.8.4 version of the Drobo Dashboard and it sees the unit just fine but doesn’t allow much to be configured. Â Maybe I …
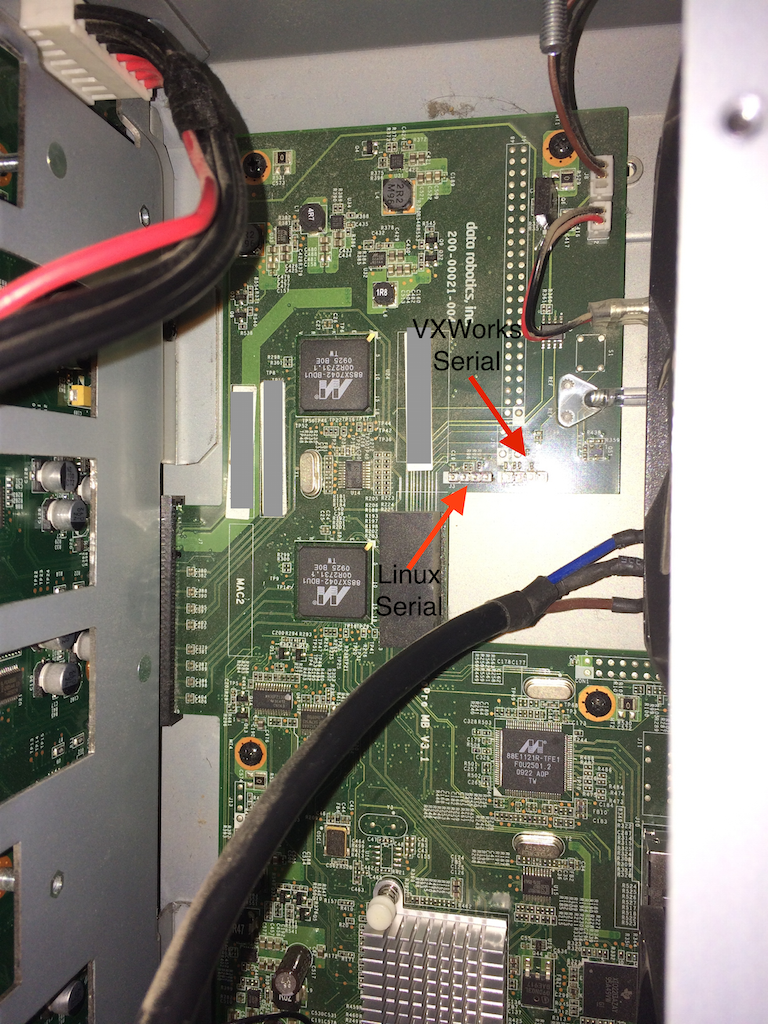
Breathing new life into my Drobo Pro
I recently saw a post somewhere that showed the internals of one of the newer high end Drobo machines. Â It appeared to use the same motherboard as the Drobo Pro I have sitting here on my desk gathering dust so I decided to take another look at what I could do with the thing. Â I …
More Yealink VP-2009 stuff
I have to admit is a little disappointed with the phone when I got it. Â I updated the firmware as far as it would allow me, but the more recent versions of the software would not install 🙁 Â After a bit of googling I found that there was supposedly a procedure for updating the old …
Yealink VOIP phone back doors
Yesterday I took delivery of a Yealink VP-2009 VIOP phone. Â I was hoping it would be a nicer phone than it actually turned out to be. Â I have a Yealink T38G and was really happy with it. Â Unfortunately a lot of the features I like in the T38G are not present in the VP-2009. Ah …
Success!
Time for bed. Â I’ve successfully hacked an app I need for work to do something it is not supposed to do 🙂 Â A little reverse engineering, byte patching and single stepping through machine code and I now have it being quite naughty 🙂
Hopper Disassembler
I’ve been using a new disassembler a lot over the last couple of weeks called Hopper. Â I’m finding it to be well worth the money. Â So much so that I initially purchased it through the Apple App store, and then purchased it again directly from the developer so I could get access to the latest …