Yesterday I took delivery of a Yealink VP-2009 VIOP phone. Â I was hoping it would be a nicer phone than it actually turned out to be. Â I have a Yealink T38G and was really happy with it. Â Unfortunately a lot of the features I like in the T38G are not present in the VP-2009. Ah well, live and learn I guess 😉
To the meat of it. Â When I plugged the new VP-2009 in to my network and attempted to configure it there was a weird caching issue with my browser as it took the same IP address as the old T38G which resulted in an error page being shown. Â Initially I thought the phone by broken in some strange way, so I started to investigate a firmware download for the phone. Â After extracting the firmware using binwalk I found the HTML for the web interface and found that there is a back door that allows arbitrary commands to be executed on the phone. Â The first thing I did was remove the password on the root user (passwd -d root) so I was able to telnet into the device. Â Once on the device I was able to poke around and see all sorts of interesting stuff.
I was interested to see if there was anything like this back door in the T38G. Â It turns out there is, although it isn’t as easy to use as the one in the VP-2009. Â There is a hidden page that allows the telnet server to be turned on, and the same code can be exploited to remove the root user password 🙂

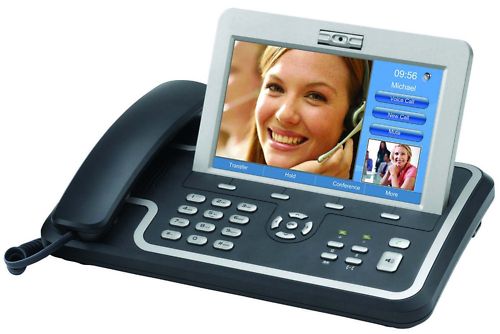
The big screen looks good.
It doesn’t have as many buttons as the T38G. Can you try to use a Pi and make an expansion like the EXP39 external call book?
Good work Daniel! I don’t mind doing the grunt work myself, but would you share what the hidden page was? I have about 40 of these phones. I am looking to get them tightly integrated into our Spiceworks database, but of course need to get at least telnet going to start breaking them down. Thanks.
Daniel hi,
i also have a Vp 2009 yealink video phone (128mb) version which i tried to update firmware 40.
The update process broke and now i only can access network page.
TFT its also working but it ask for V40 files which its not suppose to load on the 128mb version and everytime i try to update it fails.
do you have ay suggestion in order to recover the phone?
@Kyle The hidden page is available at http://
/cgi-bin/cgiServer.exx?page=hide.htm on the v40 firmware. From memory it is a little different in the older firmware, but since I don’t have one with that firmware any more I can’t remember what it is.@orange DIGITAL, I think your only option is to restore the older firmware using the TFTP interface. If your phone doesn’t have 256mb or more RAM and you try to run the newer OS you’re in for problems. I imagine it might be possible to run a swap file, but I suspect that will not run very well 😉
Hello,
thanks for this great page, I have a T21 phone, and don’t know how to enable telnet/ssh on the phone.
Could you please guide me?
Regards
Hi, Daniel
How to Reset password of admin Yealink VP- 2009 . I forget my admin password of Yealink VP-2009, I try press “OK” button 30 sec and try admin : admin . Please help me about this…
Hello Daniel! Thanks for sharing your experience with Yealink VOIP phone back doors. I appreciate your work! Keep it up!!